Wukong Enterprise Membership Grain Consumption
Documentation page: Wukong Enterprise Membership Grain Consumption
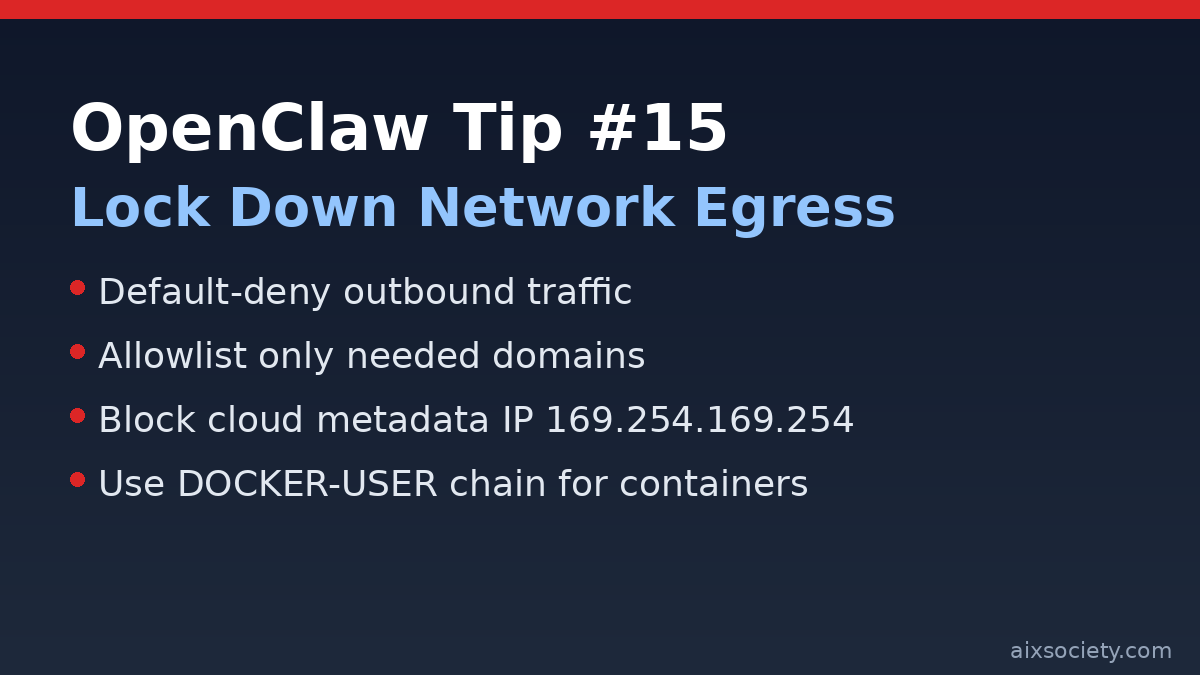
When you give OpenClaw access to tools (web, APIs, shells, connectors), you also give it paths out of your environment. The simplest way to reduce the blast radius of mistakes and prompt-injection outcomes is to restrict where your OpenClaw host (or containers) can send traffic.
Even if your prompts are solid, an agent can still leak data by POSTing it to an attacker-controlled endpoint or by accidentally querying sensitive instance metadata. A default-deny outbound policy forces you to explicitly approve destinations, making exfiltration materially harder.
Start with the minimum list. If something breaks, add a single domain, then re-test.
How you do this depends on your deployment (cloud firewall, host firewall, Kubernetes NetworkPolicy, etc.). The key pattern is:
Cloud metadata services live at 169.254.169.254 on many providers. If OpenClaw can reach it, it may unintentionally expose instance credentials. One simple host-level block is:
sudo iptables -A OUTPUT -d 169.254.169.254 -j DROPThen verify your rule is active:
sudo iptables -L -n -vDocker rewrites iptables rules; the recommended place for your own restrictions is DOCKER-USER (evaluated before Docker’s chains). Block metadata for container traffic like this:
sudo iptables -I DOCKER-USER -d 169.254.169.254 -j DROP
sudo iptables -L DOCKER-USER -n -vSource: DataCamp’s OpenClaw security best-practices guide (https://www.datacamp.com/tutorial/openclaw-security).
If you’re building a full safety posture, combine this with human confirmation for high-risk actions and strict secret handling (see other OpenClaw Tips on aixsociety.com).
Documentation page: Wukong Enterprise Membership Grain Consumption
HKOEA Consultancy
Licence No. 59684
© 2026 Artificial Intellegence Application Research Society. All rights reserved
by Originals Group – Hong Kong, Malaysia, GBA